Card security questionable as checkout extends to laptops, tablets
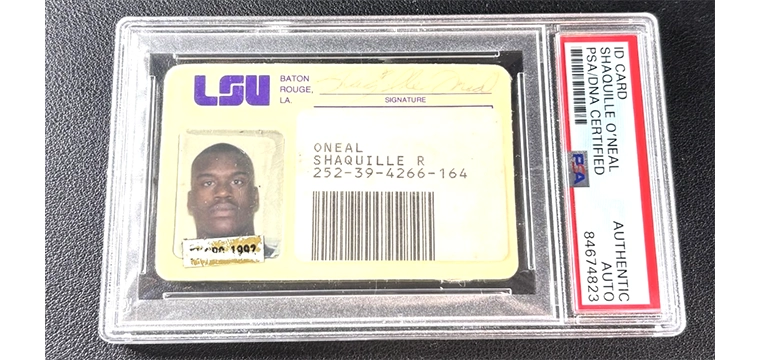
The use of a keyboard-emulating readers enable libraries to use magnetic stripe or contactless technology to push a patron ID number into an existing library check out system.
In essence, these readers connect to the computer and mimic keystrokes. It enables data to be entered to a form or application field as if it were being physically typed at the keyboard. In a library checkout system, the application waits for a fixed-length patron ID number to be presented. Using keyboard-emulating readers, this data can be typed in or provided by a bar code reader, a mag stripe reader or a contactless card reader.
For two decades, libraries have used mag stripe readers to eliminate bar codes. While it works fine, it provides little to no increase in security. This is because a mag stripe is arguably no more difficult to counterfeit than a bar code.
Contactless is another story, as it greatly ups the security ante. “Contactless keyboard-emulating readers enhance security and card utility without impacting the backend system,” explains Pawlak.
While contactless is an ideal candidate in library ID, few universities have opted to go this route.
While the immediate future likely won’t bring a tidal wave of change, there are certainly ways in which library patron ID can evolve.
“During recent campus library visits, the use of automated checkout and return systems seems to be growing in popularity,” says Pawlak. “Return stations allow patrons to present the card and then scan or tap the book and place it in the automated return.”
As these self-service solutions proliferate, the need for higher security from the patron ID grows. Contactless brings two benefits to solutions where staff is not involved.
First, it is easy for the student or patron to present the card as the reader does not require a specific orientation or swipe. It can simply be held within range. More importantly, however, contactless is vastly more difficult to counterfeit.
In traditional check out environments, library staff takes possession of and physically scans the ID card. This process entails at least a rudimentary visual inspection, and the photo must match the presenter. Even if staff is not vigorously validating the ID, this chance that it may occur is enough to ward off many would-be fraudsters.
When the human factor is removed and self check out is used, only the identification technology and number need to be valid. A blank white card with a counterfeit bar code or mag strip could be passable.
Perhaps this trend coupled with the need to protect the high value laptops and tablets that are offered by modern libraries, will drive the bar code off the card in favor of a more secure option.