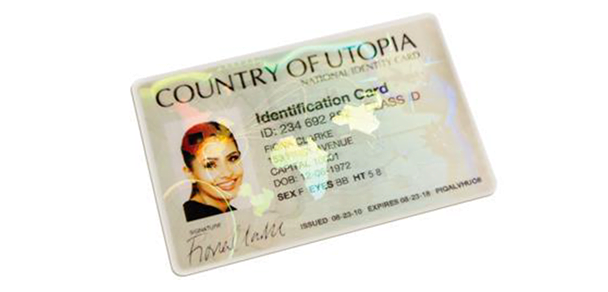
The technology may predate the widespread deployment of televisions, but holograms for secure authentication are still standing strong among document security features. And it seems that strength will continue even as digital and mobile ID technologies gain more popularity with governments, financial institutions, corporations, schools and others.
The hologram is still the only technology available today that is able to offer three levels of security – covert, overt and forensic – in a single solution
“The hologram appears to certainly be one of the security features of choice for safeguarding the critical personal data in a passport or on an ID card against tampering, alteration, forgery or counterfeiting,” reads a recent white paper from ITW Security Division entitled “The Hologram—Still Going Strong.” It dates the emergence of the hologram to 1947, with the first ID document containing a hologram debuting in 1984, on the U.N. passport. “Although its use over the years has changed from being the only authentication device used on a banknote or in a secure document to potentially one of a number today, it is by far still the most accepted and admired (document security feature).”
Consider these statistics from ITW:
So what accounts for the continued dependence on this decades-old secure authentication technology even as biometric ID systems gain popularity? Depth and flexibility, says Joanne Ogden, global sales manager for the ITW Security Division. “The hologram is still the only technology available today that is able to offer three levels of security (overt, covert and forensic) in a single solution,” she says. “Hologram manufacturers constantly watch their market to identify the techniques used by counterfeiters and ensure holography integrates additional technology solutions to counter them.”
Even so, holograms face challenges as ID technology and consumer behavior evolve. “The main challenges are for holography to integrate well with other electronic technologies such as mobile ID, and above all remain aware of competing, disruptive solutions and counterfeiting technology,” Ogden says. “By keeping focused on the market place and the problems faced, holographic technology can be adapted to remain truly relevant, protecting documents from counterfeit and aiding authentication.”
Hologram users should replace them with updated versions every five years to ensure the value as a document security feature doesn’t lag from complacency
Adapting to new threats means keeping up with the latest equipment, she adds. “Dot Matrix equipment for producing standard kinetic and colorful holograms is commercially available, so hologram manufacturers invest in the latest manufacturing techniques to produce features such as no color or movement that standard Dot Matrix equipment simply cannot produce,” she says. “Counterfeiters generally only see Level 1 features and therefore do not know about the Level 2 or 3 features, let alone have the ability to try and replicate them.”
Hologram users should replace them with updated versions every five years to ensure the value as a document security feature doesn’t lag from complacency. “Those authenticating holograms look less and less at the detail of the entire hologram as time progresses, and it is in situations like this that would be counterfeiter can try to simulate Level 1 features, often badly, but enough to fool somebody at first glance,” Ogden explains. “Hologram designs need to be kept current and fresh—integrating the latest security features—to ensure they remain the security feature of choice.”
It seems holograms for secure authentication still have a promising future ahead. “Hologram technology will remain strong,” she says. “Digital technology is good and a great add on to physical IDs with hologram technology, but digital technology is complementary rather than a replacement. Digital technology requires power and this leads to issue when power isn’t available. Electricity cuts at border control or no battery power in handheld devices mean authentication applications won’t work.”
To explore the past, present and future of hologram technology and its role as a leading document security feature, check out the free white paper from ITW. It is part of a series of resources on advanced card materials and embedded security features available via the same link. Check it out online.