 By Jerry Banks and Les G. Thompson, co-authors of RFID Applied
By Jerry Banks and Les G. Thompson, co-authors of RFID Applied
The most basic radio frequency identification solution is made up of three main hardware components. These components are the RFID tag, the RFID reader, and the antenna. This is, of course, an over simplification of what it takes to apply today's RFID technology to a real world problem, but these are the fundamental building blocks. Understanding the fundamentals of RFID is the key that allows practitioners to be successful in their application of the technology. Even though this article does not discuss the software required to interpret and make use of the RFID data, its role in a complete RFID solution is vital.
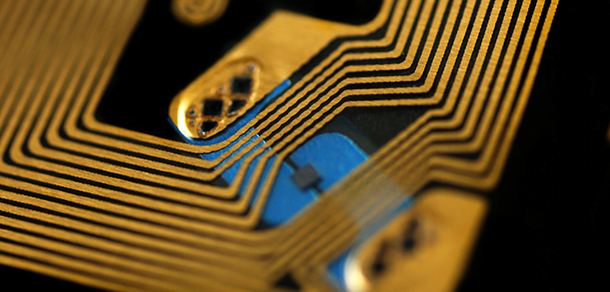
The components of the basic RFID tag are an integrated circuit (IC), an antenna, and the substrate that holds it all together. The IC is responsible for controlling the tag; much like a CPU controls a desktop computer. The IC controls what is broadcast from the tag, processes commands received from the reader via the antenna, and manages any peripherals such as temperature and pressure sensors. The antenna plays multiple roles in most RFID tags. It is responsible for receiving and transmitting data from and to the reader, and, in the case of passive type RFID tags, they collect the energy required to power the tag. Passive tags power themselves off of the energy they collect from high gain antennas that are connected to the RFID reader; therefore, they must be in close proximity to the RFID reader's antenna in order to collect enough energy to function.
RFID tags with onboard batteries are known as active tags. Unlike passive tags, they transmit their data even when they are not in close proximity to an RFID reader. In most cases, active tags can be read at a longer distance than passive tags. There is a hybrid tag known as the semi-active tag. It has an onboard battery just like the active tag, but it will only transmit when it is in close proximity to the reader.
RFID tags may transmit many different pieces of data, but the most fundamental piece of data is the tag's unique identifier. The unique identifier is, in most cases, associated with a real world asset that is to be tracked. The unique identifier is used as the key that identifies information about an asset in a database in most applications. Tags may also transmit state information or telemetry such as temperature or humidity if they have the sensors to collect this type of information. Most passive tags do not have peripheral functionality due to the power limitations of not having an onboard battery.
The RFID reader is sometimes referred to as the interrogator. The reader receives all of the data that the tags are transmitting. The data is then passed on to software that makes use of the data. The tags that are in close enough proximity to a reader are referred to as the reader's "tag population." As a reader's tag population grows, the density of tags around the reader also grows, and the reader may require more time to read all of the tags in its vicinity. This is due to the fact that if all the tags transmit at the same time, the reader will not be able to separate their data into discreet transmissions, so it is important that the tags do not transmit all at once.
Passive tag readers select subsets of the population to query over time until beacons from all of the tags in the population have been received. Most active tag readers do not control the sampling of the tag population like passive readers do. Active tags beacon at a pseudorandom interval to avoid transmission collision with other tags. Anti-collision algorithms such as the ALOHA algorithm determine when the tag will beacon. The ALOHA algorithm assigns transmission time slots to each tag. The name ALOHA is not an acronym, but was given its name because it was developed at the University of Hawaii. The ALOHA algorithm is a common anti-collision algorithm that is used by many RF applications, not only RFID. Over time, the randomization of the tag transmissions will ensure that the transmissions from all the tags are eventually received. There exists a threshold where the tag density is so great that it cannot be guaranteed that all the tags will be sampled in a timely manner. The tag density maximum is different for each RFID tag and reader manufacturer. Some manufacturers even allow the anti-collision algorithm to be changed based on the needs of the solution.
The importance of the antenna that is connected to the reader cannot be underestimated. In a passive RFID solution, the antenna must be sensitive enough to receive the RFID tag transmissions and it must also be powerful enough to power the tags. Passive tag reader antennas may be deployed in many different configurations depending on the application. A portal configuration is the most common type. Portals place an antenna on each side of the tag's path (i.e., at a loading dock door or on an assembly line). Sometimes, a portal configuration may also affix antennas on the top and bottom of the pathway to completely surround the tag's path, thus increasing the chances of reading the tag as it passes through the portal.
Antennas used in active tag applications must solve a different set of problems. Many times, active tags are used in a real-time location system (RTLS). An RTLS is used to track tagged assets as they move through a building, yard, or supply chain. Active reader antennas are usually installed in the middle of the desired coverage area. For example, an antenna could be placed in the ceiling in the middle of a room. This antenna could then read all of the tags in the room. Because of the increased transmission power of most active RFID tags, when compared to passive tags, the antenna may also read tags outside of the room. Transmissions from tags in adjacent rooms, hallways, or in a room immediately above the antenna in a multistory building may be inadvertently received by the antenna. This is known as "bleeding coverage." Most RTLS's require that the coverage be well defined to a single room or to a zone within a room. To resolve this issue, the correct antenna must be selected that meets the needs of the RF environment. Antennas must provide smooth and consistent input to the RFID reader in order for it to efficiently decode the tags' transmissions. Bad input will yield bad results, especially in RTLS's.
In the words of Scotty from Star Trek, "You can't bend the laws of physics, Captain!" Even though RFID practitioners are bound by the laws of physics, they can make smart decisions about what components they choose and how they are deployed.
This article is the first in an ongoing series that will explain the principles of RFID. The series is developed for RFIDNews by Jerry Banks, an Independent Consultant working in Atlanta Georgia and Les G. Thompson, Chief Technical Officer for Lost Recovery Network, Inc., Atlanta, Georgia. They are two of four co-authors of the book RFID Applied, John Wiley, 2007, ISBN-10 0471793655; ISBN-13 978-041793656.